Core to Cloud Blog
Our hot takes on the latest cybersecurity developments, technologies and challenges.
An immediate cybersecurity threat
What do you need to know? A recent report from the UK's Joint Committee on the National Security Strategy has sounded a clarion call about the nation's cybersecurity vulnerabilities. The alarming revelation is that the UK could be paralysed "at any moment" by a...
Latest:
An immediate cybersecurity threat
Apr 3, 2024 | Core to Cloud News, Frameworks
What do you need to know? A recent report from the UK's Joint Committee on the National Security Strategy has sounded a clarion call about the nation's cybersecurity vulnerabilities. The alarming revelation is that the UK could be paralysed "at any moment" by a...
All
Core to Cloud News
AI News
Core to Cloud Services
Core to Cloud Technologies
Unraveling the Midnight Blizzard Attack on Microsoft
How can your business use SaaS security applicatio...
Your choice for Cyber Security Support – Core to Cloud
Comparing outsourced cybersecurity support service...


Lessons from Real-World Cybersecurity Failures
Here are some tips on how to establish a strong fo...
Bringing you innovative NDR and SIEM Security
Core to Cloud Partners with Cybersecurity Innovato...
The Ultimate Guide: Enhancing Third-Party Risk Management
Introduction to third-party risk management Given ...

Core to Cloud Partners with Cybersecurity Innovator AppOmni to Enable Comprehensive SaaS Security
The new strategic arrangement gives organisations ...

Shine a Light into the Dark – Cyber Threat Intelligence
Let's Shine a Light into the Dark - Cyber Threat I...

Comprehensive Guide to Managed Detection and Response (MDR)
Introduction to MDR Managed Detection and Response...

How Clean Are You? – Basic Cyber Hygiene
Introduction to cyber hygiene: In today's fast-pac...
Securing Tomorrow: Cybersecurity Trends and Innovations in 2024
Introduction: Navigating the Evolving Cybersecurit...
An Increased Need for Configuration – GYPTOL
In the fast-paced world of cybersecurity, where th...
Addressing the Cyber Security Talent Shortage: An Industry Perspective
As an industry, we need to address the shortage of...

Core to Cloud Partners with Panorays to Protect Businesses from Supply Chain Compromise
Cirencester, 11th December 2023 – Core to Cloud,...
Ways to reduce security spend without compromising security
Tighter Budgets: How to tighten the belt without l...

Safeguarding the Festive Season: Fortifying Against Holiday Cyber Threats
As the joyous spirit of the holiday season ...
Cyber Awareness: 4 Actionable Steps to Enhance Your Cybersecurity
Introduction: Cyber Awareness and Your Digital Sec...
The Cyber Games: May Cyber Security Be Ever in Your Favour
Welcome, esteemed tributes of the corporate arena,...
Guarding Your Business Against Holiday Season Cyber Threats
Unmasking the Hidden Cybersecurity Threats Lurking...
Understanding the Digital Operational Resilience Act (DORA) EU Regulation 2022/2554
The Digital Operational Resilience Act (DORA) is a...
Improving Endpoint Security and Quick Remediation during M&A Processes with GYTPOL
Enhancing M&A Security with GYTPOL: Your Endpo...
Threads App Launch: Unravelling Privacy Concerns
Threads App Privacy Concerns Unveiled: What You Ne...
How AI is Upgrading Scams: Unveiling the Dark Side of Artificial Intelligence
You must have seen the rise in AI-driven technolog...
Embracing AI in Cyber security: Enhancing Cyber Calmness and Empowering Human Experts
AI is not replacing you. The person using AI to he...
Penetration Testing Cost 2023: How Much To Secure Your Business
Penetration testing, also referred to as ethical h...
The Importance of Cyber Security for Successful Movie Premieres: Protecting Barbie and Oppenheimer
This year’s highly-acclaimed movies, the glitzy ...
Penetration Testing Cost 2023: Estimating Penetration Testing Costs
Considering the overall cost of penetration testin...
ISO 27001 Cost 2023 – How Much To Get Certified?
ISO 27001 is a globally recognised standard for ma...
ISO 27001 – How To Be Prepared in 2023
ISO certification can bring benefits such as impro...
A Comprehensive Comparison of CIS, NIS2, and DORA
Introduction to Cybersecurity Frameworks Acronyms ...
Cyber Security Software: Why “One and Done” Doesn’t Cut it
You have bought all of your licences. Spent hour...
The Great Cyber Security Debate: New Software vs. New Staff
It is a common discussion that we have been a part...
Safeguarding Networks: Illumio’s Innovative Approach to Defending Against Email Compromise Attacks
75% of companies have experienced an increase in e...
Dormant Accounts: The Hidden Danger in Your Cyber Security
Just like a forgotten lunchbox that was last seen ...
How AI is Revolutionising Cybersecurity: Trends and Implications
The field of cybersecurity is an ever-changing lan...
Protect Your Privacy: Understanding TikTok’s Data Concerns
TikTok…. TikTok…. TikTok…. Is time running o...
There are no limits at Core to Cloud
To those that are new to our communities or networ...
Understanding the output compared to your input within cyber security
You have brought your cyber security licences and ...
Tips and Resources for Women in Tech in 2023
As you might know, the 8th of March is Internation...
Let’s Close the Cyber Skills Gap for Good
Identifying the cybersecurity skills gap in your w...
Unleashing the Power of ChatGPT: A Comprehensive Exploration
Introduction Chat GPT stands as a pinnacle of lang...
What does ROI look like in Cybersecurity?
In business terms ROI (Return on investment) is th...
Why more protection isn’t always better 😉
Oi, you. Mind out of the gutter. This is a serious...
Let’s Bust Some Jargon: Core to Cloud Style!
Words, words everywhere…. Big words, smaller wor...
Why don’t we say “Dark Web” anymore?
We have all seen news outlets detailing the latest...
A whirlwind of celebrations, awards, and growth
As 2022 begins to end we wanted to take a moment t...
An Interview with Irina Nesterovsky, Chief Research office at KELA
In our next interview within our wonderful women i...
An Interview with Vanessa Cardwell, Marketing Director at Bite IT
It is truly wonderful to be on this journey highli...
Achieve Infinite Potential with Extreme Networks
The pandemic highlighted weaknesses within our exi...
The Cloud Platform that prioritises protection
Lacework is a data-driven platform that gives you ...
An office with history, the new home of CTC!
We have been working on something incredibly speci...
SentinelOne, the future of AV and EDR Technology
Let’s take a trip back in time…. The history...
Let iboss keep your hybrid team safe and secure
As we were catapulted into a new way of hybrid wor...
The History of AV (anti-virus)/ EDR technology
Started out with First Generation, old legacy AV s...
Core to Cloud receives award for ‘Best Cyber Company 2022’
TechSPARK UK Awards It’s time to polish the trop...
Cylera announces new NHS Cyber Alerts Dashboard
According to a report from Clearswift, 67% of UK h...
Safeguarding What Matters Most: Healthcare Cybersecurity The Cylera x Extreme Networks Integration
Cyberattacks are no longer the reserve of individu...
Vectra AI: The Power of AI Threat Detection
Cybersecurity professionals face an unprecedented ...
Iboss: Leading Innovation in Cloud Security
Cyberattacks are among the biggest concerns for bu...
Digital Health Rewired 2022 returned with a festival designed to help you achieve your digital future.
Rewired 2022 was reimagined as the premier UK even...

Abnormal: the next generation of email security
You’d be pretty annoyed if you got home to find ...

Key areas to protect: Remote working for the future
Zapier, Google, Twitter… carving a futuristic pa...


Core to Cloud passes ISO accreditation and Cyber Essentials Plus
We talk the talk and walk the walk...we’re delig...

Ransomware has got no match for this…
Ransomware attacks are no longer just broad, autom...

Let’s bust the PrintNightmare bug once and for all
The PrintNightmare vulnerability has been affectin...
How to protect your organisation’s attack surface
Picture the scene. You’re about to go on holiday...

Post-pandemic cybersecurity predictions
2020 irreversibly changed the global economic and ...

How Does Your Organisation Respond to Cyber Security Incidents?
The importance of Incident Response Services Incid...

Office365: Protecting the largest, most popular Saas application
Office365 is Microsoft’s fastest-growing product...



Core to Cloud partners with Immersive Labs
When it comes to cyber security awareness, it’s ...

CyCognito partners with Core to Cloud
All businesses are digital businesses, to varying ...

Securing what matters most healthcare devices ensuring patient safety
COVID-19 has accelerated the digital transformatio...


Extreme Networks partners with Core to Cloud
There’s no denying that cloud-managed network se...

Let’s talk about cybersecurity in the NHS
In the last few years alone, the healthcare indust...

The unique difference Cylera makes in medical security
‘Built with hospitals, for hospitals’, Cylera ...

The Vectra Vision: AI-driven threat detection and response
Contrary to popular belief, cybersecurity breaches...
Load More
Your choice for Cyber Security Support – Core to Cloud
Comparing outsourced cybersecurity support service...


Lessons from Real-World Cybersecurity Failures
Here are some tips on how to establish a strong fo...

How Clean Are You? – Basic Cyber Hygiene
Introduction to cyber hygiene: In today's fast-pac...
Securing Tomorrow: Cybersecurity Trends and Innovations in 2024
Introduction: Navigating the Evolving Cybersecurit...
An Increased Need for Configuration – GYPTOL
In the fast-paced world of cybersecurity, where th...
Addressing the Cyber Security Talent Shortage: An Industry Perspective
As an industry, we need to address the shortage of...
Ways to reduce security spend without compromising security
Tighter Budgets: How to tighten the belt without l...

Safeguarding the Festive Season: Fortifying Against Holiday Cyber Threats
As the joyous spirit of the holiday season ...
Cyber Awareness: 4 Actionable Steps to Enhance Your Cybersecurity
Introduction: Cyber Awareness and Your Digital Sec...
The Cyber Games: May Cyber Security Be Ever in Your Favour
Welcome, esteemed tributes of the corporate arena,...
Guarding Your Business Against Holiday Season Cyber Threats
Unmasking the Hidden Cybersecurity Threats Lurking...
Understanding the Digital Operational Resilience Act (DORA) EU Regulation 2022/2554
The Digital Operational Resilience Act (DORA) is a...
Improving Endpoint Security and Quick Remediation during M&A Processes with GYTPOL
Enhancing M&A Security with GYTPOL: Your Endpo...
Threads App Launch: Unravelling Privacy Concerns
Threads App Privacy Concerns Unveiled: What You Ne...
How AI is Upgrading Scams: Unveiling the Dark Side of Artificial Intelligence
You must have seen the rise in AI-driven technolog...
Embracing AI in Cyber security: Enhancing Cyber Calmness and Empowering Human Experts
AI is not replacing you. The person using AI to he...
Penetration Testing Cost 2023: How Much To Secure Your Business
Penetration testing, also referred to as ethical h...
The Importance of Cyber Security for Successful Movie Premieres: Protecting Barbie and Oppenheimer
This year’s highly-acclaimed movies, the glitzy ...
Penetration Testing Cost 2023: Estimating Penetration Testing Costs
Considering the overall cost of penetration testin...
ISO 27001 Cost 2023 – How Much To Get Certified?
ISO 27001 is a globally recognised standard for ma...
ISO 27001 – How To Be Prepared in 2023
ISO certification can bring benefits such as impro...
A Comprehensive Comparison of CIS, NIS2, and DORA
Introduction to Cybersecurity Frameworks Acronyms ...
Cyber Security Software: Why “One and Done” Doesn’t Cut it
You have bought all of your licences. Spent hour...
The Great Cyber Security Debate: New Software vs. New Staff
It is a common discussion that we have been a part...
Safeguarding Networks: Illumio’s Innovative Approach to Defending Against Email Compromise Attacks
75% of companies have experienced an increase in e...
Dormant Accounts: The Hidden Danger in Your Cyber Security
Just like a forgotten lunchbox that was last seen ...
How AI is Revolutionising Cybersecurity: Trends and Implications
The field of cybersecurity is an ever-changing lan...
Protect Your Privacy: Understanding TikTok’s Data Concerns
TikTok…. TikTok…. TikTok…. Is time running o...
There are no limits at Core to Cloud
To those that are new to our communities or networ...
Understanding the output compared to your input within cyber security
You have brought your cyber security licences and ...
Tips and Resources for Women in Tech in 2023
As you might know, the 8th of March is Internation...
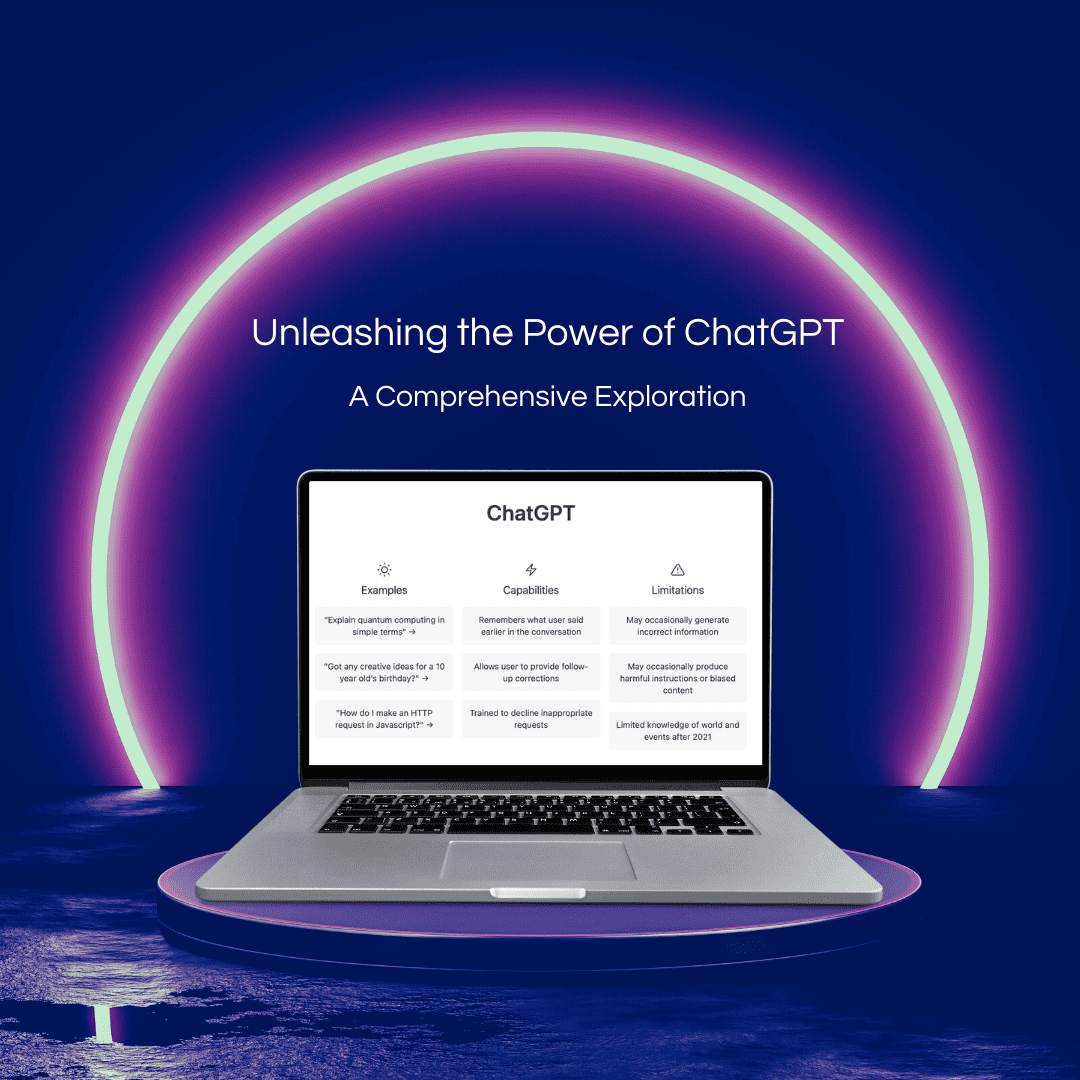
Unleashing the Power of ChatGPT: A Comprehensive Exploration
Introduction Chat GPT stands as a pinnacle of lang...
What does ROI look like in Cybersecurity?
In business terms ROI (Return on investment) is th...
Why more protection isn’t always better 😉
Oi, you. Mind out of the gutter. This is a serious...
Let’s Bust Some Jargon: Core to Cloud Style!
Words, words everywhere…. Big words, smaller wor...
Why don’t we say “Dark Web” anymore?
We have all seen news outlets detailing the latest...
A whirlwind of celebrations, awards, and growth
As 2022 begins to end we wanted to take a moment t...
An Interview with Irina Nesterovsky, Chief Research office at KELA
In our next interview within our wonderful women i...
An Interview with Vanessa Cardwell, Marketing Director at Bite IT
It is truly wonderful to be on this journey highli...
Achieve Infinite Potential with Extreme Networks
The pandemic highlighted weaknesses within our exi...
The Cloud Platform that prioritises protection
Lacework is a data-driven platform that gives you ...
An office with history, the new home of CTC!
We have been working on something incredibly speci...
SentinelOne, the future of AV and EDR Technology
Let’s take a trip back in time…. The history...
Let iboss keep your hybrid team safe and secure
As we were catapulted into a new way of hybrid wor...
Core to Cloud receives award for ‘Best Cyber Company 2022’
TechSPARK UK Awards It’s time to polish the trop...
Iboss: Leading Innovation in Cloud Security
Cyberattacks are among the biggest concerns for bu...

Abnormal: the next generation of email security
You’d be pretty annoyed if you got home to find ...


Core to Cloud passes ISO accreditation and Cyber Essentials Plus
We talk the talk and walk the walk...we’re delig...

Ransomware has got no match for this…
Ransomware attacks are no longer just broad, autom...

Let’s bust the PrintNightmare bug once and for all
The PrintNightmare vulnerability has been affectin...

Post-pandemic cybersecurity predictions
2020 irreversibly changed the global economic and ...

How Does Your Organisation Respond to Cyber Security Incidents?
The importance of Incident Response Services Incid...

Office365: Protecting the largest, most popular Saas application
Office365 is Microsoft’s fastest-growing product...



Core to Cloud partners with Immersive Labs
When it comes to cyber security awareness, it’s ...

CyCognito partners with Core to Cloud
All businesses are digital businesses, to varying ...

Securing what matters most healthcare devices ensuring patient safety
COVID-19 has accelerated the digital transformatio...


Extreme Networks partners with Core to Cloud
There’s no denying that cloud-managed network se...

Let’s talk about cybersecurity in the NHS
In the last few years alone, the healthcare indust...

The unique difference Cylera makes in medical security
‘Built with hospitals, for hospitals’, Cylera ...

The Vectra Vision: AI-driven threat detection and response
Contrary to popular belief, cybersecurity breaches...
Load More
Securing Tomorrow: Cybersecurity Trends and Innovations in 2024
Introduction: Navigating the Evolving Cybersecurit...
How AI is Upgrading Scams: Unveiling the Dark Side of Artificial Intelligence
You must have seen the rise in AI-driven technolog...
Embracing AI in Cyber security: Enhancing Cyber Calmness and Empowering Human Experts
AI is not replacing you. The person using AI to he...
How AI is Revolutionising Cybersecurity: Trends and Implications
The field of cybersecurity is an ever-changing lan...
Unleashing the Power of ChatGPT: A Comprehensive Exploration
Introduction Chat GPT stands as a pinnacle of lang...
Unraveling the Midnight Blizzard Attack on Microsoft
How can your business use SaaS security applicatio...
Your choice for Cyber Security Support – Core to Cloud
Comparing outsourced cybersecurity support service...
The Ultimate Guide: Enhancing Third-Party Risk Management
Introduction to third-party risk management Given ...

Shine a Light into the Dark – Cyber Threat Intelligence
Let's Shine a Light into the Dark - Cyber Threat I...

Comprehensive Guide to Managed Detection and Response (MDR)
Introduction to MDR Managed Detection and Response...
Bringing you innovative NDR and SIEM Security
Core to Cloud Partners with Cybersecurity Innovato...

Core to Cloud Partners with Cybersecurity Innovator AppOmni to Enable Comprehensive SaaS Security
The new strategic arrangement gives organisations ...

Shine a Light into the Dark – Cyber Threat Intelligence
Let's Shine a Light into the Dark - Cyber Threat I...

How Clean Are You? – Basic Cyber Hygiene
Introduction to cyber hygiene: In today's fast-pac...
Securing Tomorrow: Cybersecurity Trends and Innovations in 2024
Introduction: Navigating the Evolving Cybersecurit...
An Increased Need for Configuration – GYPTOL
In the fast-paced world of cybersecurity, where th...

Core to Cloud Partners with Panorays to Protect Businesses from Supply Chain Compromise
Cirencester, 11th December 2023 – Core to Cloud,...

Safeguarding the Festive Season: Fortifying Against Holiday Cyber Threats
As the joyous spirit of the holiday season ...
The Cyber Games: May Cyber Security Be Ever in Your Favour
Welcome, esteemed tributes of the corporate arena,...
Improving Endpoint Security and Quick Remediation during M&A Processes with GYTPOL
Enhancing M&A Security with GYTPOL: Your Endpo...
Penetration Testing Cost 2023: How Much To Secure Your Business
Penetration testing, also referred to as ethical h...
Penetration Testing Cost 2023: Estimating Penetration Testing Costs
Considering the overall cost of penetration testin...
Cyber Security Software: Why “One and Done” Doesn’t Cut it
You have bought all of your licences. Spent hour...
Safeguarding Networks: Illumio’s Innovative Approach to Defending Against Email Compromise Attacks
75% of companies have experienced an increase in e...
Understanding the output compared to your input within cyber security
You have brought your cyber security licences and ...
Let’s Close the Cyber Skills Gap for Good
Identifying the cybersecurity skills gap in your w...
Why don’t we say “Dark Web” anymore?
We have all seen news outlets detailing the latest...
An Interview with Irina Nesterovsky, Chief Research office at KELA
In our next interview within our wonderful women i...
Achieve Infinite Potential with Extreme Networks
The pandemic highlighted weaknesses within our exi...
The Cloud Platform that prioritises protection
Lacework is a data-driven platform that gives you ...
SentinelOne, the future of AV and EDR Technology
Let’s take a trip back in time…. The history...
Let iboss keep your hybrid team safe and secure
As we were catapulted into a new way of hybrid wor...
The History of AV (anti-virus)/ EDR technology
Started out with First Generation, old legacy AV s...
Cylera announces new NHS Cyber Alerts Dashboard
According to a report from Clearswift, 67% of UK h...
Safeguarding What Matters Most: Healthcare Cybersecurity The Cylera x Extreme Networks Integration
Cyberattacks are no longer the reserve of individu...
Vectra AI: The Power of AI Threat Detection
Cybersecurity professionals face an unprecedented ...
Iboss: Leading Innovation in Cloud Security
Cyberattacks are among the biggest concerns for bu...
Digital Health Rewired 2022 returned with a festival designed to help you achieve your digital future.
Rewired 2022 was reimagined as the premier UK even...

Abnormal: the next generation of email security
You’d be pretty annoyed if you got home to find ...

Key areas to protect: Remote working for the future
Zapier, Google, Twitter… carving a futuristic pa...
How to protect your organisation’s attack surface
Picture the scene. You’re about to go on holiday...

Office365: Protecting the largest, most popular Saas application
Office365 is Microsoft’s fastest-growing product...


Core to Cloud partners with Immersive Labs
When it comes to cyber security awareness, it’s ...

Securing what matters most healthcare devices ensuring patient safety
COVID-19 has accelerated the digital transformatio...

Let’s talk about cybersecurity in the NHS
In the last few years alone, the healthcare indust...

The unique difference Cylera makes in medical security
‘Built with hospitals, for hospitals’, Cylera ...

The Vectra Vision: AI-driven threat detection and response
Contrary to popular belief, cybersecurity breaches...
Load More