Consultative Service
Discover Potential Security Vulnerabilities with our Gap Analysis.
Cybersecurity Gap Analysis
Our Gap Assessment leverages the Assets, Technologies, and Processes that will be evaluated against the 18 Controls outlined by the Centre for Internet Security (CIS).
Address the vulnerabilities in your security system, determine the most significant risks to your cybersecurity.
The key to a successful cybersecurity program lies in comprehending your current state. By conducting a thorough gap analysis, we can provide you with a prioritised road map of requirements tailored to your specific risks and needs.
Our Service
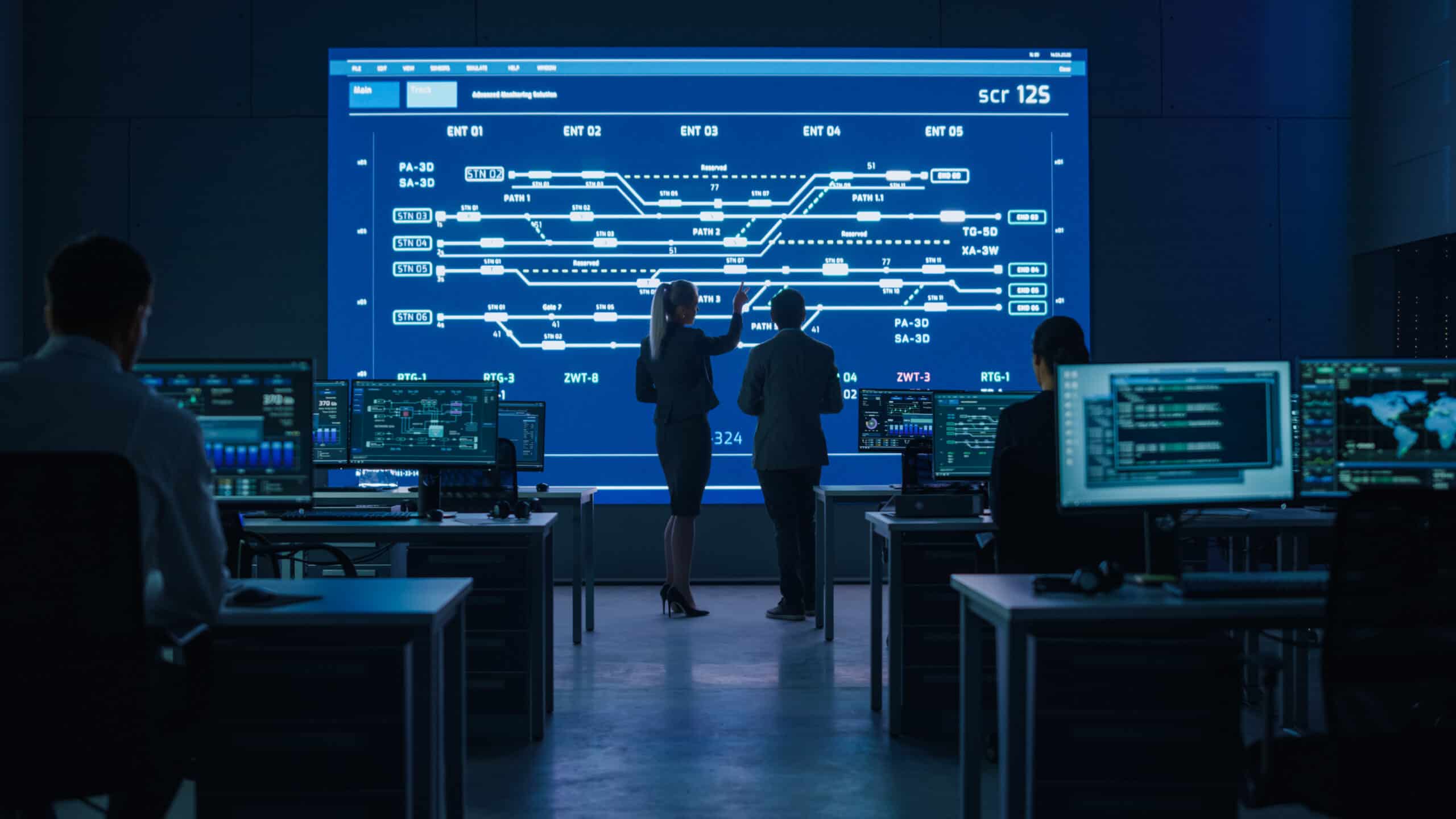
We will conduct a collaborative discovery service with you and your key stakeholders.
The service will be a comprehensive information-gathering exercise that covers Networks, Devices, Identity and Access Management, Email and Web Services, Data, Assets and App Development, and Security Operations.
The Assets, Technologies and Processes will be measured against the 18 x Controls specified by the Centre for Internet Security (CIS).
A Gap Analysis report with a Red, Amber, and Green status will be delivered to the customer, marking the starting point of the security posture improvement process.
A Governance plan will be discussed with you.
Conduct a Full Gap Analysis
In the ever-changing cybersecurity landscape, staying ahead of threats is not just an advantage; it's a necessity.
The UK Government's latest report shows that 83% of small businesses, 91% of medium businesses and 96% of large enterprises report that cybersecurity is high or very high on their priorities.
Benefits of taking our GAP Analysis
Improve your cybersecurity posture
Reduce potential risks to your
business
Exceed
compliance
standards
Increased competitive advantage
The Impacts of Data Breaches on Businesses
GBP 3.7 Million
The global average cost of a data breach in 2023 was GBP 3.7 million, a 15% increase over 3 years.
51%
of organisations are preparing to increase investment in security due to a breach, including incident response planning and exercising, employee training, and threat detection and response tools.
GBP 1.5 Million
The average savings for organisations that use security AI and automation extensively is GBP 1.5 million compared to organisations that don’t.
According to the Cost of a Data Breach Report 2023 by IBM
Why Every Business Needs a Cyber Security Gap Analysis...
Gaining a deep understanding of your organisation’s security posture is essential to have critical visibility and insights into potentials risks.
An assessment will provide a detailed view of digital assets, infrastructure, information systems, networks, applications, and configurations. Two key success factors of achieving a thorough audit are governance and controls.
A one-off audit is vital, but even more important is to ensure a robust governance process is in place to flag changes that could compromise security. Using controls will provide benchmarks and references to widely adopted standards, driving improvements across the board.
Frequently Asked Questions
What is included in a Gap Analysis?
- Overview of the process and the steps
- Initial Questions via Questionnaire
- Gap Analysis Calls
- On-Site Visit to Main UK Site.
- Reporting
- Report Addendum aligning gap analysis results to Cyber Essentials
Why the CIS Framework?
The CIS framework is the gold standard in cybersecurity. Developed by a global community of experts, it provides a prioritised, pragmatic approach to fortifying digital defences.
Our gap analysis delves deep into this framework, ensuring your organisation aligns with the best practices endorsed by cybersecurity professionals worldwide.
How do you find gaps in my security?
Security gaps can be discovered through a comprehensive security gap analysis tailored to the unique requirements of your business and industry. We prioritise identifying these gaps to ensure the robustness of your security measures. Which assesses and addresses vulnerabilities, safeguarding your organisation against potential threats.
How long does it take?
Our Gap Analysis typically requires 3-4 working days to complete, allowing for flexibility in scheduling over a few weeks or condensing into a shorter timeframe. We understand the importance of time efficiency when it comes to evaluating your gaps, ensuring a comprehensive assessment within the specified period.
Why is it important to complete a Gap Analysis?
In addition to protecting their data, companies face the constant challenge of compliance and regulations. Failure to comply with ISO27001, Cyber Essentials, and other standards can be costly and damaging to a company’s market reputation. Conversely, demonstrating a highly secure and compliant environment can be a business benefit and an opportunity for growth, as new customers recognise the lower risk of doing business.